Have a Question?
How to Setup pfBlockerNG
Overview
pfBlockerNG is a very powerful package for pfSense® which provides advertisement and malicious content blocking along with geoIP-blocking capabilities.
Installing pfBlockerNG
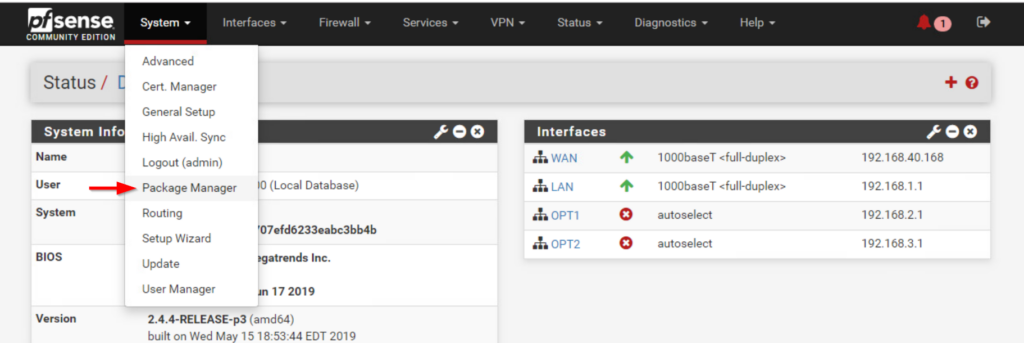
- Access the pfSense WebGUI (default 192.168.1.1)
- Click on the System tab, then Package Manager
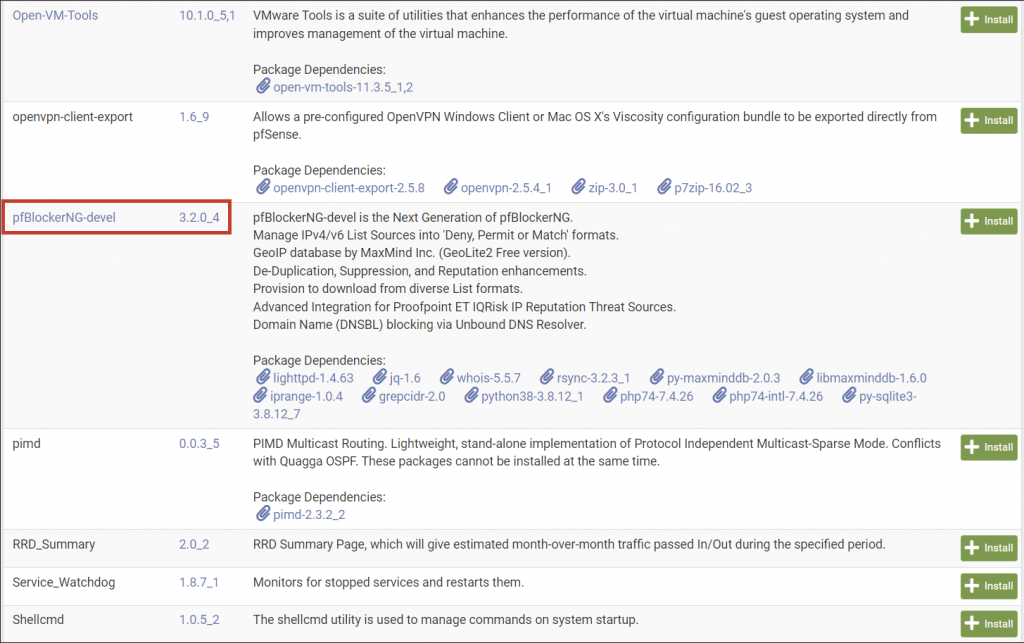
- From the Package Manager menu select the Available Packages tab
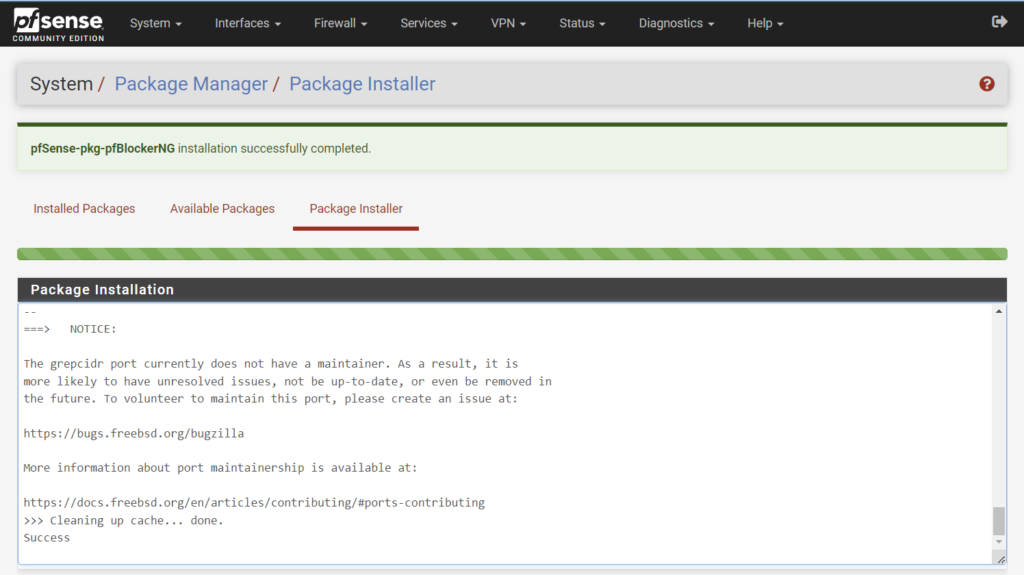
- Scroll down and find pfBlockerNG-devel and click Install
- Note: Clicking on the package name will take you to Netgate's Documentation for pfBlockerNG
- Verify pfBlockerNG is now installed by going to the Firewall drop down menu
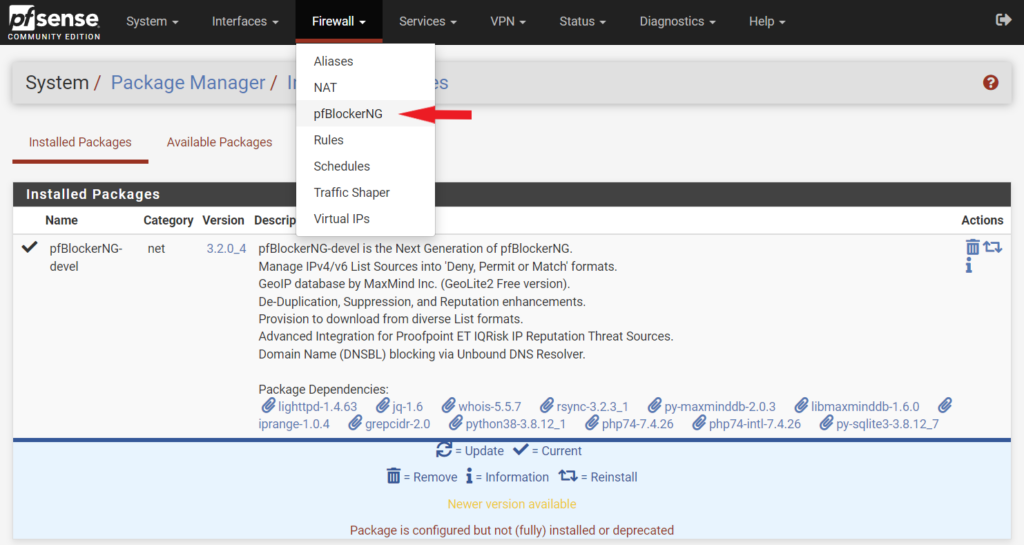
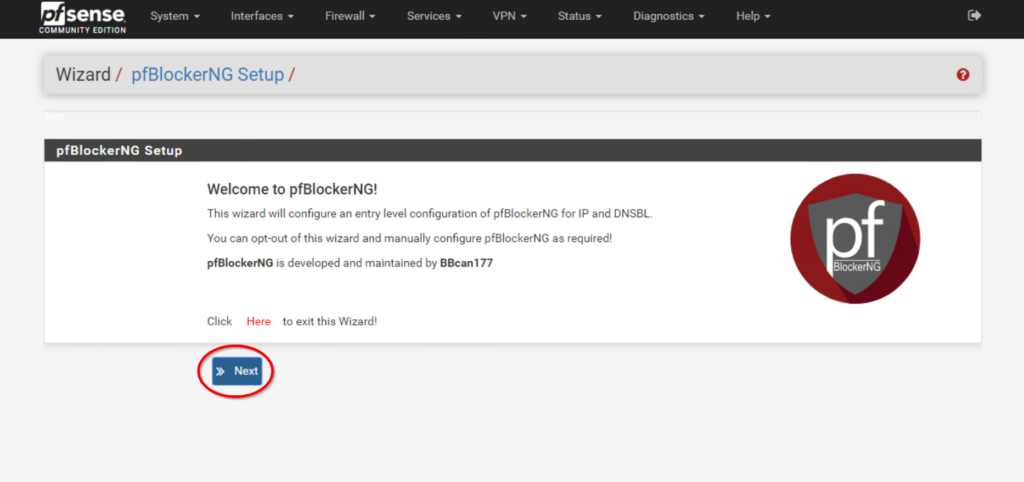
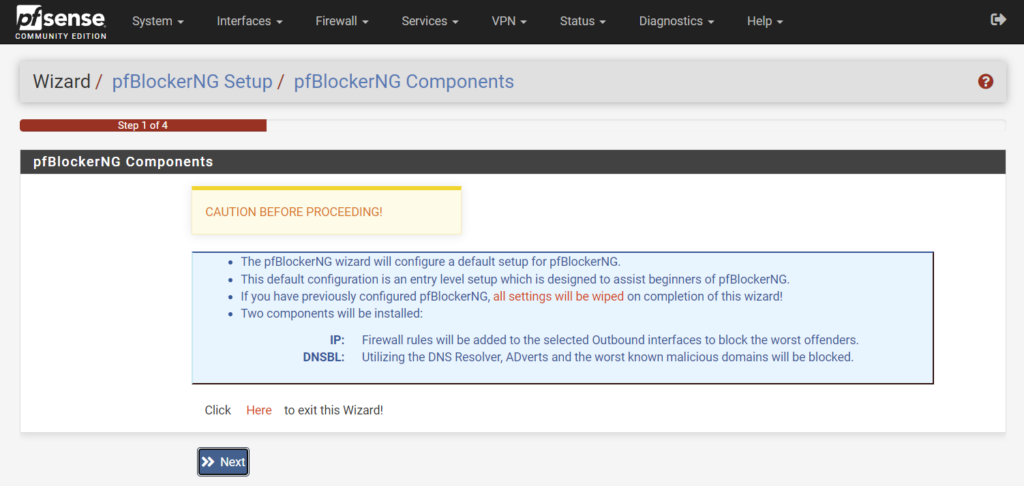
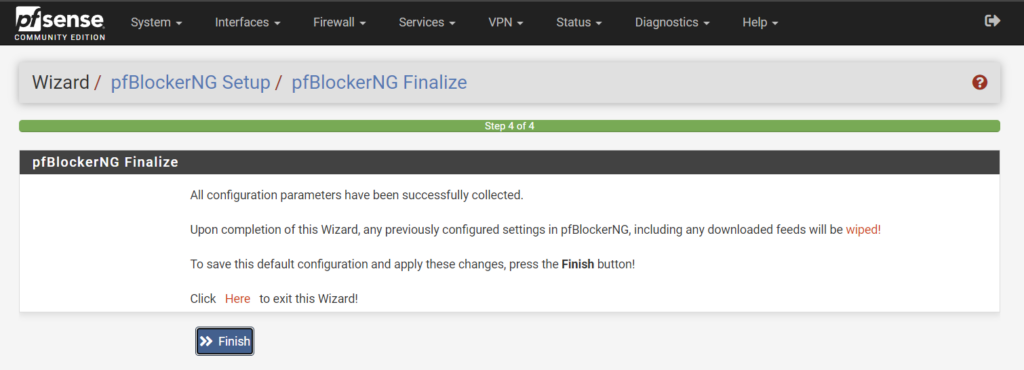
- Open the pfBlockerNG menu and start the wizard
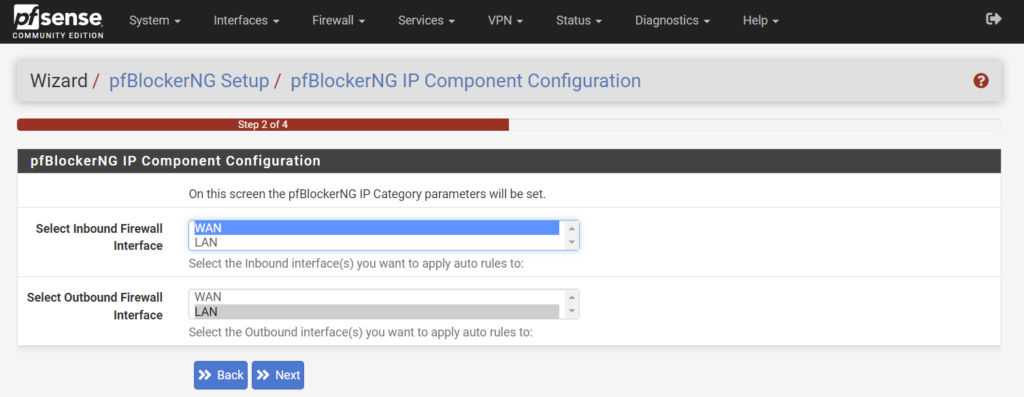
- At the Component Configuration page of the wizard select the WAN interface for inbound. For outbound typically LAN is used.
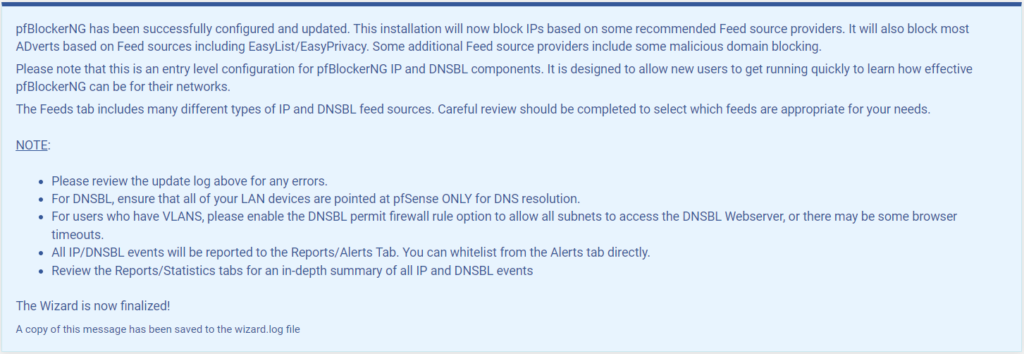
- Click Finish and allow pfBlocker to update
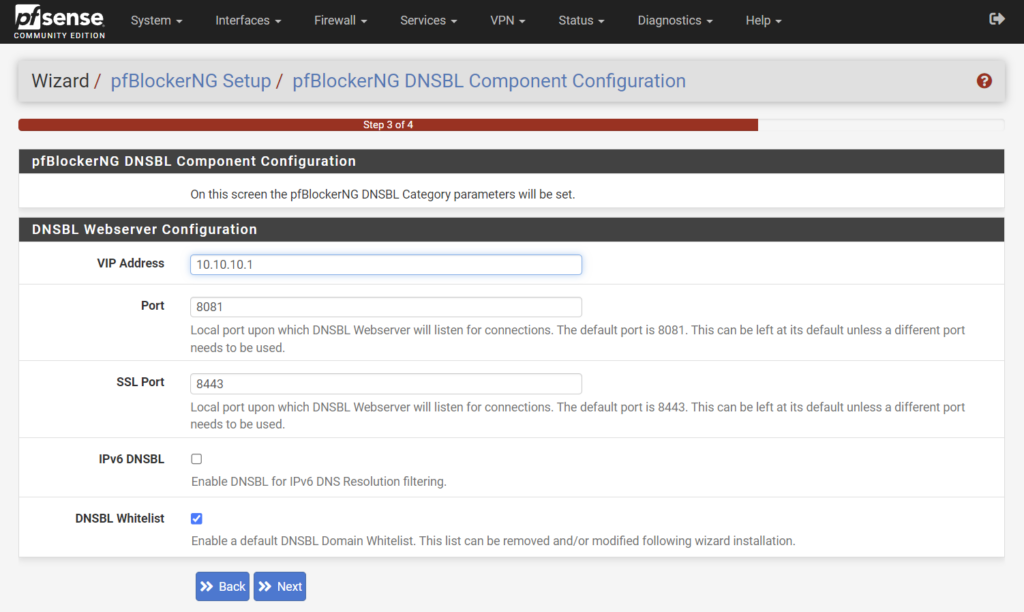
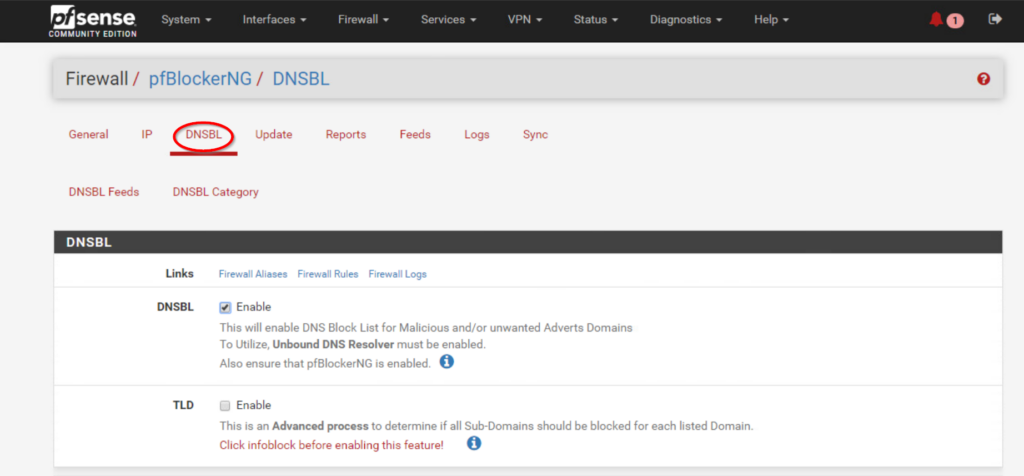
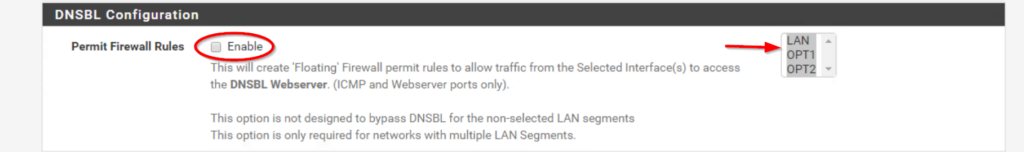
- If you would like multiple LAN segments to be included in with DNSBL check the setting Permit Firewall Rules and select the interface (ctrl+click) you would like included.
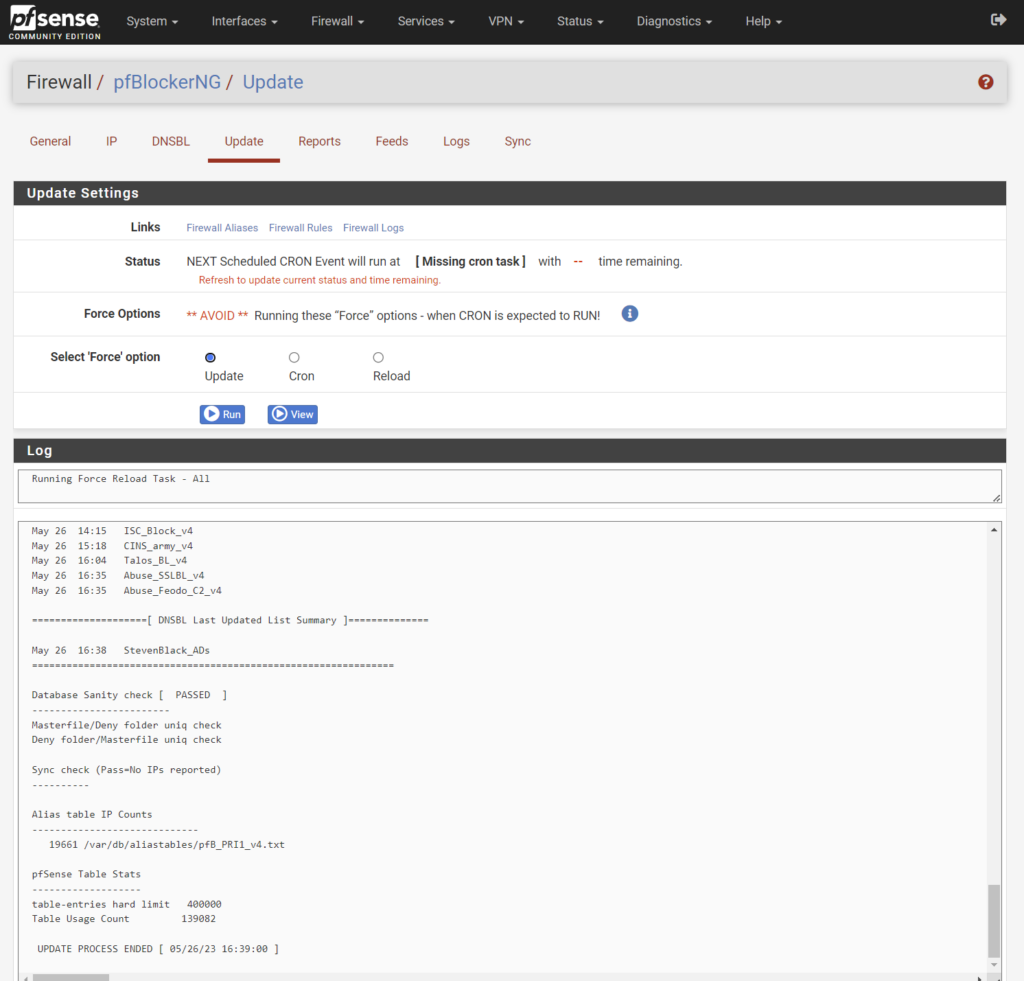
- By Default pfBlockerNG will setup basic advertisement and IP blocking from the following feeds:
- Spamhaus_Drop_v4
- Spamhaus_eDrop_v4
- ET_Block_v4
- ET_Comp_v4
- CINS_army_v4
- ISC_Block_v4
- Abuse_SSLBL_v4
- Abuse_Feodo_C2_v4
- Talos_BL_v4
- StevenBlack_ADs
- Once the feeds are added, it is important to reload and update
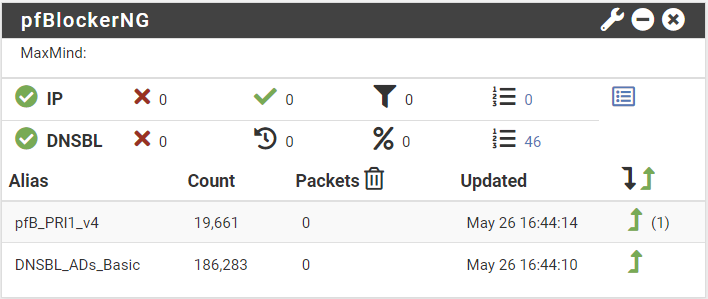
- Now browse a few websites and then check the pfSense dashboard to verify the pfBlockerNG widget is showing data
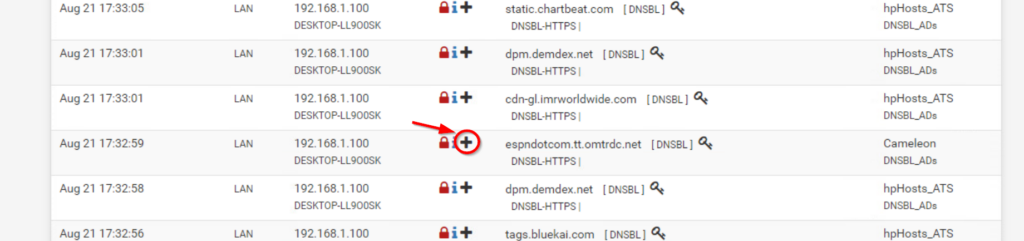
You might come across false positives possibly breaking certain sites. The solution is adding addresses to a Whitelist
- To add an item to the whitelist access the pfBlockerNG Reports either by clicking on one of the packet stats (arrow below) or through the pfBlocker menu
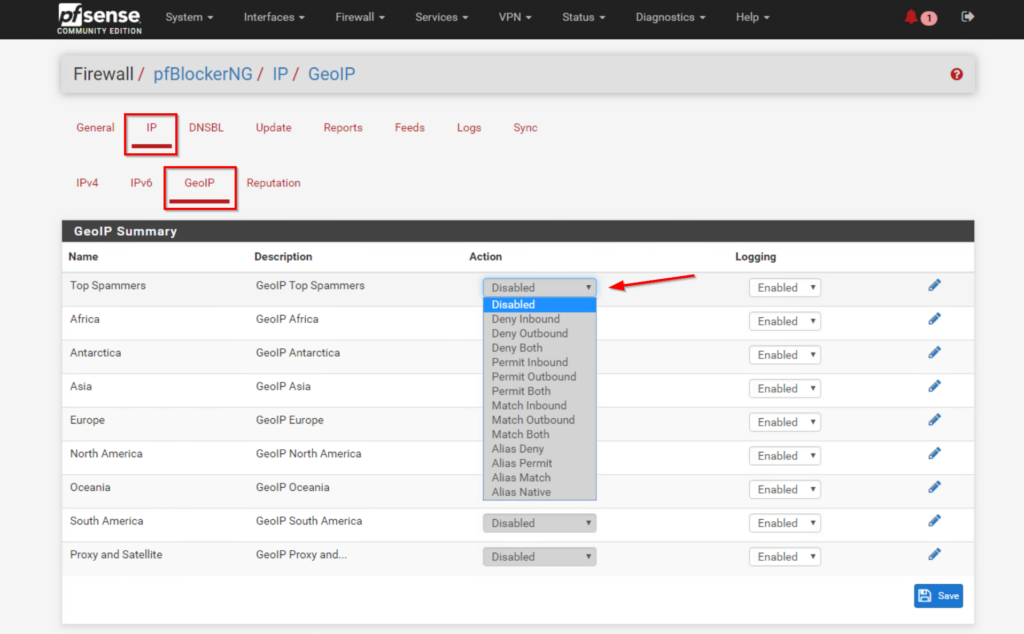
pfBlocker also has built in GeoIP blocking. This allows you control over geographic regions connecting to your network. You can find this in the pfBlockerNG menu under IP>GeoIP. Careful blocking too much, websites host content and media on servers around the world. Unintentionally blocking some of these IP addresses could result in broken sites or unavailable downloads.
You should now have network wide advertisement and malicious content blocking. If you need additional assistance, please feel free to reach out: support@protectli.com. You can find more information about pfSense on the Vault in our Knowledge Base, or at pfSense.org
