Have a Question?
How to Configure pfSense® CE for 4G LTE Failover
How to Configure pfSense® CE for 4G LTE Failover
pfSense® CE is an open source routing and firewall software which is based on FreeBSD. It has a variety of packages easily downloaded and configurable within the GUI itself. https://www.pfsense.org/getting-started/ There are multiple articles regarding pfSense® CE on the Protectli Knowledge Base at this link. This article describes how to configure pfSense® CE for 4G LTE Failover using Protectli 4G LTE Products and Service. The example uses pfSense ® CE version 2.4.4-p3. Protectli 4G LTE Products and Services can be found at this link. 4G LTE Failover with the Vault requires at least 3 Ethernet ports, 1 each for WAN, LAN, and OPT1. Therefore a 4 or 6 port version of the Vault is required. In addition, it requires that the Protectli 4G LTE modem has been provisioned and is active on the cellular network. This article assumes the default configuration of pfSense ® CE with the WAN getting an IP address via DHCP and the default LAN static IP address of 192.168.1.1 and is a DHCP server.
Enable Interfaces
By default the WAN interface is configured to receive an IP address via DHCP and the LAN interface has static IP address 192.168.1.1 and is a DHCP server. Only the OPT1 interface needs to be configured.
- Install pfSense ® CE on the Vault. (See Knowledge Base link if needed)
- Connect the WAN and LAN ports to the devices or ports that they are normally connected to
- Connect the OPT1 port to the LAN port of the 4G LTE modem
- Browse to the pfSense ® CE GUI and login
- Select Interfaces->Interface Assignments
- Add OPT1 and select the default Network port (em2 or igb2)
- Select "OPT1" to configure the port
- Select General Configuration->Enable->Enable interface check box
- Select General Configuration->IPv4 Configuration Type->DHCP to get the IP address of OPT1 from the 4G LTE modem
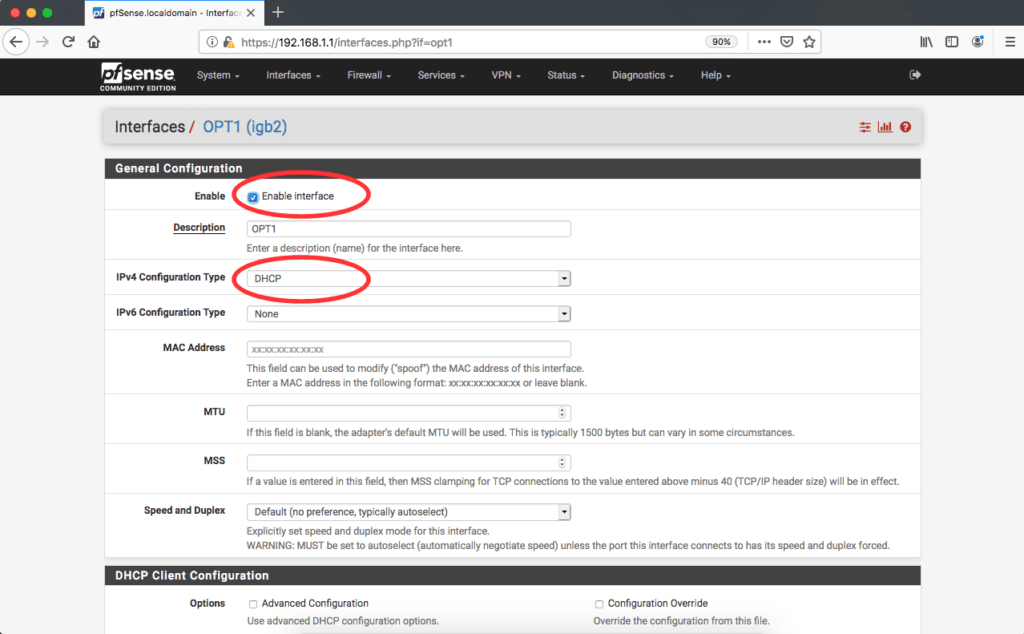
- Select the SAVE button at the bottom of the page
- Select the APPLY CHANGES button when it appears at the top of the page
- Select Status->Dashboard and verify that the Dashboard is displayed
- Select the red "+" sign in the upper right corner of the GUI and enable the "Interfaces" widget
- Verify the WAN, LAN, and OPT1 interfaces are up with IP addresses in the "Interfaces" widget
- Select the red "+" sign in the upper right corner of the GUI and enable the "Traffic Graphs" Widget
- Verify the Traffic Graphs widget is displayed and shows WAN, LAN, and OPT1
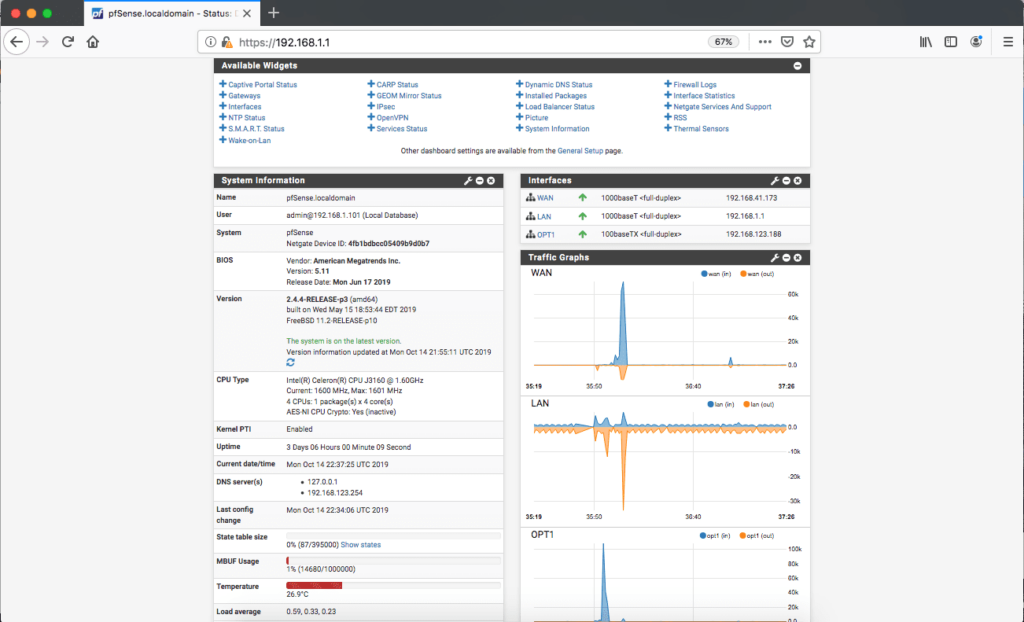
At this point the interfaces have been enabled and are active. Now the WAN and OPT1 interfaces need to be configured as Gateways and form a Gateway Group so that they can failover and revert.
Configure Gateways
- Select System->Routing->Gateways
- Verify WAN_DHCP is displayed
- Select Edit Icon
- Set Edit Gateway->Monitor IP to 8.8.8.8 This is the Google DNS address. pfSense ® CE will monitor this address to determine if this connection is up
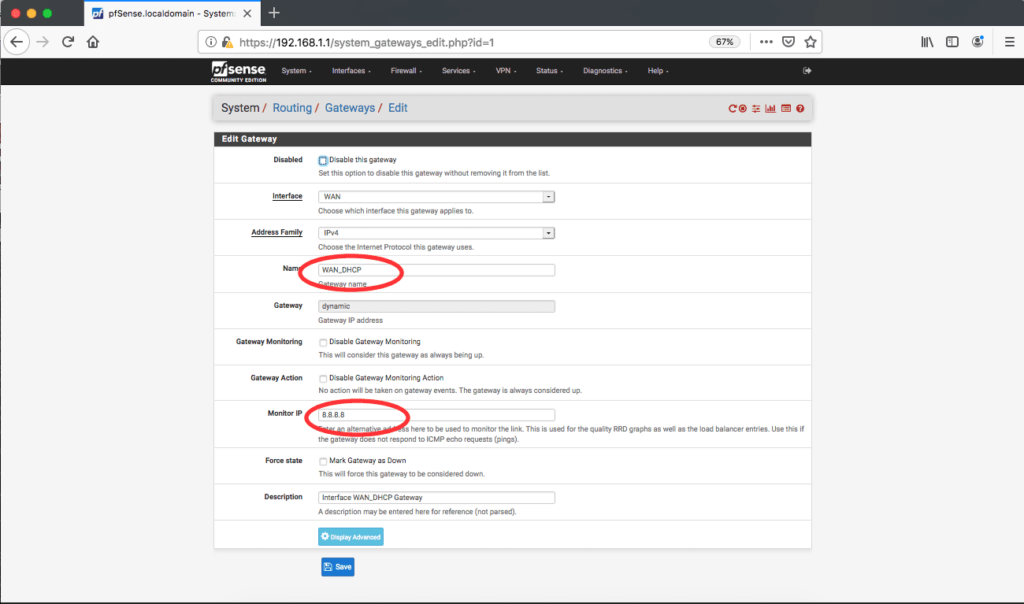
- Select the SAVE button at the bottom of the page
- Select the APPLY CHANGES button when it appears at the top of the page
- Select System->Routing->Gateways
- Select ADD button
- Add OPT1 Interface
- Verify the Name is OPT1_DHCP
- Set Edit Gateway->Monitor IP to 1.1.1.1 This is the Cloudflare DNS address. pfSense ® CE will monitor this address to determine if this connection is up
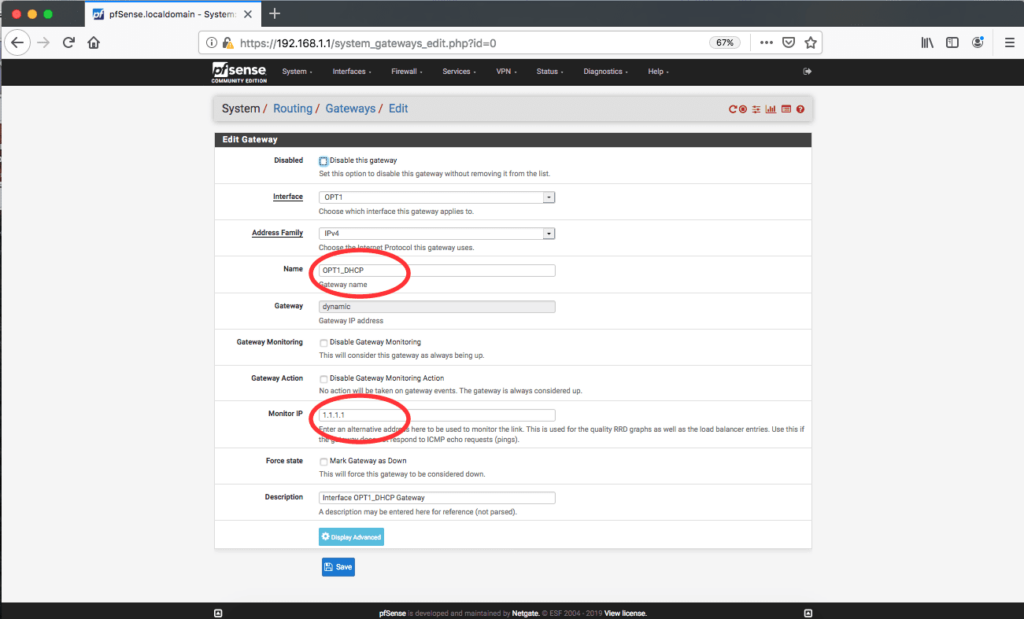
- Select the SAVE button at the bottom of the page
- Select the APPLY CHANGES button when it appears at the top of the page
At this point the WAN and OPT1 interfaces have been configured as Gateways. Now they need to be configured as a Gateway Group so that they can operate as a single entity, failover and revert.
Configure Gateway Groups
- Select System->Routing->Gateway Groups
- Select ADD button
- Set Edit Gateway Group Entry->Group Name to "Group_WAN_OPT1" or desired name
- Set Edit Gateway Group Entry->Gateway Priority->WAN_DHCP->Tier to "Tier 1" (highest priority)
- Set Edit Gateway Group Entry->Gateway Priority->OPT1_DHCP->Tier to "Tier 5" (lowest priority)
- Set Edit Gateway Group Entry->Trigger Level to "Member Down" (Failover when link is down)
- Set Edit Gateway Group Entry->Description if desired
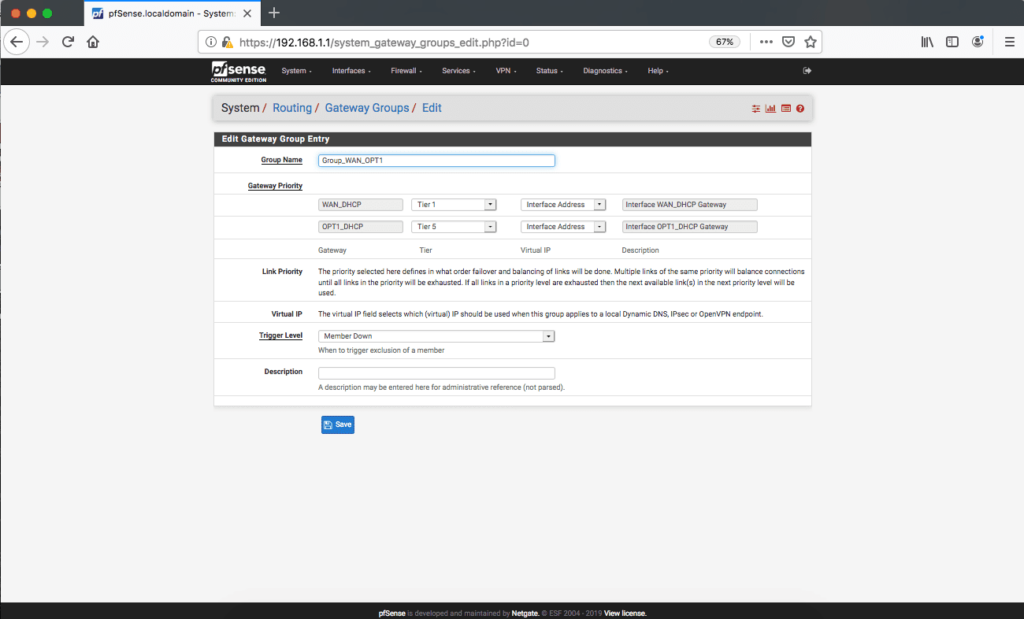
- Select the SAVE button at the bottom of the page
- Select the APPLY CHANGES button when it appears at the top of the page
At this point interfaces are enabled, Gateways configured and a Gateway Group with WAN and OPT1 has been configured. The last step is to set the LAN Firewall rule to select the Gateway Group as the Gateway, rather than treat WAN and OPT1 as individual interfaces.
Configure LAN Firewall
- Select Firewall->Rules->LAN
- Select Edit for "Default allow LAN to any rule"
- Select ADVANCED button
- Set Advanced Options->Gateway to "Group_WAN_OPT1" or the name given to the Gateway Group above
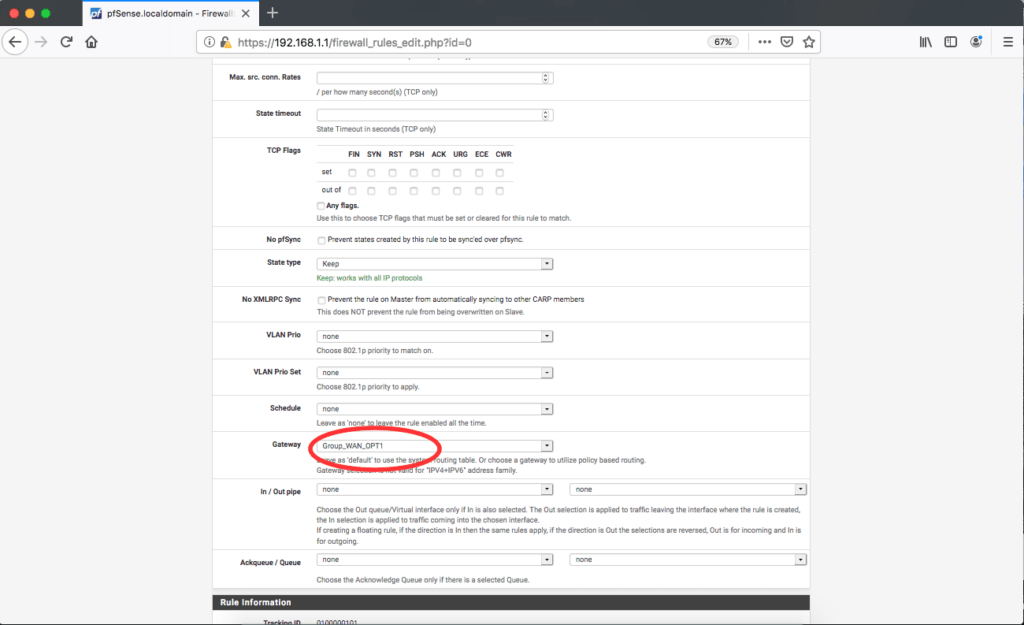
- Select the SAVE button at the bottom of the page
- Select the APPLY CHANGES button when it appears at the top of the page
At this point, everything has been configured. We need to verify the Gateway status.
Verify Gateway Status
- Select Status->Gateways
- Verify WAN_DHCP and OPT1_DHCP Gateways are online
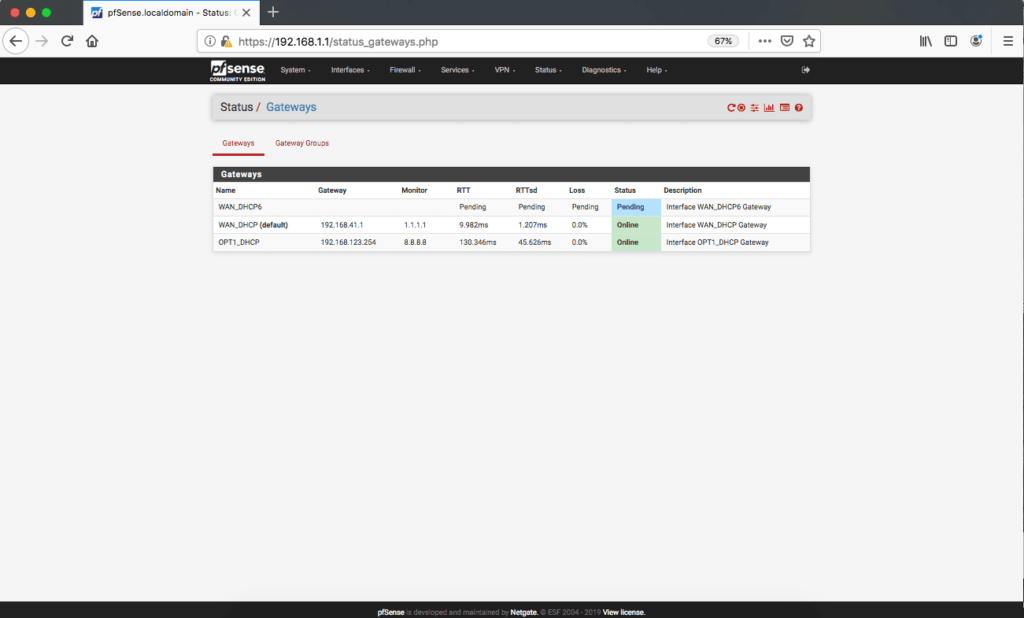
At this point, everything has been configured, gateways are up. We need to verify that the 4G LTE Failover functions as desired.
Verify 4G LTE Failover
The Vault has been configured to failover from WAN port to OPT1 port in the event the WAN port goes down. When the WAN port comes back, traffic should revert back to the WAN port. pfSense® CE monitors the gateway connectivity via the "Monitor IP" address configured earlier to determine whether the connection is "up" or not. "Up" means full connectivity to the Monitor IP address. This means that even if the Ethernet link is up, but the unit cannot ping the Monitor IP address, the Gateway is considered down and will failover to another gateway in the Gateway Group. The detection time and failover is typically on the order of 15-20 seconds because pfSense® CE monitors the connectivity at the system level as opposed to just the Ethernet link level.
The following steps can be used to verify the 4G LTE Failover is working correctly.
- Generate significant traffic from the LAN port to the Internet, for example, using a PC connected to the LAN port, browse to a web site and play a video
- Select Dashboard and monitor the Traffic Graphs
- Verify the WAN and LAN ports have similar high levels of traffic
- Disconnect the WAN port from the Vault
- Verify the video continues to play
- Verify the OPT1 and LAN ports have similar high levels of traffic and the WAN port shows no traffic (as noted, about 15-20 seconds to failover)
- Reconnect the WAN port to the Vault
- Verify the video continues to play
- Verify the WAN and LAN ports have similar high levels of traffic and the OPT1 port shows little traffic (about 15-20 seconds to revert)
At this point, 4G LTE Failover should be up and running on The Vault. However, if you experience any issues, please feel free to reach out to us: You can submit a ticket here, or find more information in our Knowledge Base.
